Table of Contents
Samba-3 supports NT4-style domain trust relationships. This is a feature that many sites will want to use if they migrate to Samba-3 from an NT4-style domain and do not want to adopt Active Directory or an LDAP-based authentication backend. This chapter explains some background information regarding trust relationships and how to create them. It is now possible for Samba-3 to trust NT4 (and vice versa), as well as to create Samba-to-Samba trusts.
The use of interdomain trusts requires use of winbind, so the
winbindd daemon must be running. Winbind operation in this mode is
dependent on the specification of a valid UID range and a valid GID range in the smb.conf file.
These are specified respectively using:
idmap uid = 10000-20000 |
idmap gid = 10000-20000 |
The range of values specified must not overlap values used by the host operating system and must not overlap values used in the passdb backend for POSIX user accounts. The maximum value is limited by the upper-most value permitted by the host operating system. This is a UNIX kernel limited parameter. Linux kernel 2.6-based systems support a maximum value of 4294967295 (32-bit unsigned variable).
Note
The use of winbind is necessary only when Samba is the trusting domain, not when it is the trusted domain.
Samba-3 can participate in Samba-to-Samba as well as in Samba-to-MS Windows NT4-style trust relationships. This imparts to Samba scalability similar to that with MS Windows NT4.
Given that Samba-3 can function with a scalable backend authentication database such as LDAP, and given its ability to run in primary as well as backup domain control modes, the administrator would be well-advised to consider alternatives to the use of interdomain trusts simply because, by the very nature of how trusts function, this system is fragile. That was, after all, a key reason for the development and adoption of Microsoft Active Directory.
MS Windows NT3/4-type security domains employ a nonhierarchical security structure. The limitations of this architecture as it effects the scalability of MS Windows networking in large organizations is well known. Additionally, the flat namespace that results from this design significantly impacts the delegation of administrative responsibilities in large and diverse organizations.
Microsoft developed Active Directory Service (ADS), based on Kerberos and LDAP, as a means of circumventing the limitations of the older technologies. Not every organization is ready or willing to embrace ADS. For small companies the older NT4-style domain security paradigm is quite adequate, and so there remains an entrenched user base for whom there is no direct desire to go through a disruptive change to adopt ADS.
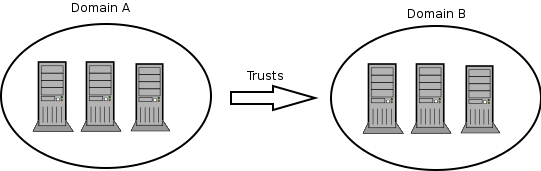
With Windows NT, Microsoft introduced the ability to allow different security domains to effect a mechanism so users from one domain may be given access rights and privileges in another domain. The language that describes this capability is couched in terms of trusts. Specifically, one domain will trust the users from another domain. The domain from which users can access another security domain is said to be a trusted domain. The domain in which those users have assigned rights and privileges is the trusting domain. With NT3.x/4.0 all trust relationships are always in one direction only, so if users in both domains are to have privileges and rights in each others' domain, then it is necessary to establish two relationships, one in each direction.
Further, in an NT4-style MS security domain, all trusts are nontransitive. This means that if there are three domains (let's call them red, white, and blue), where red and white have a trust relationship, and white and blue have a trust relationship, then it holds that there is no implied trust between the red and blue domains. Relationships are explicit and not transitive.
New to MS Windows 2000 ADS security contexts is the fact that trust relationships are two-way by default. Also, all inter-ADS domain trusts are transitive. In the case of the red, white, and blue domains, with Windows 2000 and ADS, the red and blue domains can trust each other. This is an inherent feature of ADS domains. Samba-3 implements MS Windows NT4-style interdomain trusts and interoperates with MS Windows 200x ADS security domains in similar manner to MS Windows NT4-style domains.
There are two steps to creating an interdomain trust relationship. To effect a two-way trust relationship, it is necessary for each domain administrator to create a trust account for the other domain to use in verifying security credentials.
For MS Windows NT4, all domain trust relationships are configured using the Domain User Manager. This is done from the Domain User Manager Policies entry on the menu bar. From the menu, select . Next to the lower box labeled Permitted to Trust this Domain are two buttons, and . The button will open a panel in which to enter the name of the remote domain that will be able to assign access rights to users in your domain. You will also need to enter a password for this trust relationship, which the trusting domain will use when authenticating users from the trusted domain. The password needs to be typed twice (for standard confirmation).
A trust relationship will work only when the other (trusting) domain makes the appropriate connections with the trusted domain. To consummate the trust relationship, the administrator launches the Domain User Manager from the menu selects Policies, then select Trust Relationships, and clicks on the button next to the box that is labeled Trusted Domains. A panel opens in which must be entered the name of the remote domain as well as the password assigned to that trust.
A two-way trust relationship is created when two one-way trusts are created, one in each direction. Where a one-way trust has been established between two MS Windows NT4 domains (let's call them DomA and DomB), the following facilities are created:
DomA (completes the trust connection)
TrustsDomB.DomA is the
Trustingdomain.DomB is the
Trusteddomain (originates the trust account).Users in DomB can access resources in DomA.
Users in DomA cannot access resources in DomB.
Global groups from DomB can be used in DomA.
Global groups from DomA cannot be used in DomB.
DomB does appear in the logon dialog box on client workstations in DomA.
DomA does not appear in the logon dialog box on client workstations in DomB.
Users and groups in a trusting domain cannot be granted rights, permissions, or access to a trusted domain.
The trusting domain can access and use accounts (users/global groups) in the trusted domain.
Administrators of the trusted domain can be granted administrative rights in the trusting domain.
Users in a trusted domain can be given rights and privileges in the trusting domain.
Trusted domain global groups can be given rights and permissions in the trusting domain.
Global groups from the trusted domain can be made members in local groups on MS Windows domain member machines.
This description is meant to be a fairly short introduction about how to set up a Samba server so that it can participate in interdomain trust relationships. Trust relationship support in Samba is at an early stage, so do not be surprised if something does not function as it should.
Each of the procedures described next assumes the peer domain in the trust relationship is controlled by a Windows NT4 server. However, the remote end could just as well be another Samba-3 domain. It can be clearly seen, after reading this document, that combining Samba-specific parts of what's written in the following sections leads to trust between domains in a purely Samba environment.
In order to set the Samba PDC to be the trusted party of the relationship, you first need to create a special account for the domain that will be the trusting party. To do that, you can use the smbpasswd utility. Creating the trusted domain account is similar to creating a trusted machine account. Suppose, your domain is called SAMBA, and the remote domain is called RUMBA. The first step will be to issue this command from your favorite shell:
root#smbpasswd -a -i rumbaNew SMB password:XXXXXXXXRetype SMB password:XXXXXXXXAdded user rumba$
where -a means to add a new account into the
passdb database and -i means to “create this
account with the Interdomain trust flag”.
The account name will be “rumba$” (the name of the remote domain).
If this fails, you should check that the trust account has been added to the system
password database (/etc/passwd). If it has not been added, you
can add it manually and then repeat the previous step.
After issuing this command, you will be asked to enter the password for the account. You can use any password you want, but be aware that Windows NT will not change this password until 7 days following account creation. After the command returns successfully, you can look at the entry for the new account (in the standard way as appropriate for your configuration) and see that the account's name is really RUMBA$ and it has the “I” flag set in the flags field. Now you are ready to confirm the trust by establishing it from Windows NT Server.
Open User Manager for Domains and from the menu, select
. Beside the Trusted domains list box,
click the button. You will be prompted for the trusted domain name and the
relationship password. Type in SAMBA, as this is the name of the remote domain and the password used at the
time of account creation. Click on and, if everything went without incident, you
will see the Trusted domain relationship successfully established message.
This time activities are somewhat reversed. Again, we'll assume that your domain controlled by the Samba PDC is called SAMBA and the NT-controlled domain is called RUMBA.
The very first step is to add an account for the SAMBA domain on RUMBA's PDC.
Launch the Domain User Manager, then from the menu select , . Now, next to the Trusted Domains box, press the button and type in the name of the trusted domain (SAMBA) and the password to use in securing the relationship.
The password can be arbitrarily chosen. It is easy to change the password from the Samba server whenever you want. After you confirm the password, your account is ready for use. Now its Samba's turn.
Using your favorite shell while logged in as root, issue this command:
root# net rpc trustdom establish rumba
You will be prompted for the password you just typed on your Windows NT4 Server box.
An error message, "NT_STATUS_NOLOGON_INTERDOMAIN_TRUST_ACCOUNT,"
that may be reported periodically is of no concern and may safely be ignored.
It means the password you gave is correct and the NT4 server says the account is ready for
interdomain connection and not for ordinary connection. After that, be patient;
it can take a while (especially in large networks), but eventually you should see
the Success message. Congratulations! Your trust
relationship has just been established.
Note
You have to run this command as root because you must have write access to
the secrets.tdb file.
Although Domain User Manager is not present in Windows 2000, it is also possible to establish an NT4-style trust relationship with a Windows 2000 domain controller running in mixed mode as the trusting server. It should also be possible for Samba to trust a Windows 2000 server; however, more testing is still needed in this area.
After creating the interdomain trust account on the Samba server
as described previously, open Active Directory Domains and Trusts on the AD
controller of the domain whose resources you wish Samba users to have access to. Remember that since NT4-style
trusts are not transitive, if you want your users to have access to multiple mixed-mode domains in your AD
forest, you will need to repeat this process for each of those domains. With Active Directory
domains and trusts open, right-click on the name of the Active Directory domain that will trust
our Samba domain and choose , then click on the
Trusts tab. In the upper part of the panel, you will see a list box labeled
Domains trusted by this domain: and an Add... button next to it.
Press this button and, just as with NT4, you will be prompted for the trusted domain name and the relationship
password. Press OK and after a moment, Active Directory will respond with
The trusted domain has been added and the trust has been verified. Your
Samba users can now be granted access to resources in the AD domain.
Interdomain trust relationships should not be attempted on networks that are unstable or that suffer regular outages. Network stability and integrity are key concerns with distributed trusted domains.
Browsing from a machine in a trusted Windows 200x domain to a Windows 200x member of a trusting Samba domain, I get the following error:
The system detected a possible attempt to compromise security. Please ensure that you can contact the server that authenticated you.
The event logs on the box I'm trying to connect to have entries regarding group policy not being applied because it is a member of a down-level domain.
If there is a computer account in the Windows 200x domain for the machine in question, and it is disabled, this problem can occur. If there is no computer account (removed or never existed), or if that account is still intact (i.e., you just joined it to another domain), everything seems to be fine. By default, when you unjoin a domain (the Windows 200x domain), the computer tries to automatically disable the computer account in the domain. If you are running as an account that has privileges to do this when you unjoin the machine, it is done; otherwise it is not done.
If you use the smbldap-useradd script to create a trust
account to set up interdomain trusts, the process of setting up the trust will
fail. The account that was created in the LDAP database will have an account
flags field that has [W ], when it must have
[I ] for interdomain trusts to work.
Here is a simple solution. Create a machine account as follows:
root# smbldap-useradd -w domain_name
Then set the desired trust account password as shown here:
root# smbldap-passwd domain_name\$
Using a text editor, create the following file:
dn: uid=domain_name$,ou=People,dc={your-domain},dc={your-top-level-domain}
changetype: modify
sambaAcctFlags: [I ]
Then apply the text file to the LDAP database as follows:
root# ldapmodify -x -h localhost \
-D "cn=Manager,dc={your-domain},dc={your-top-level-domain}" \
-W -f /path-to/foobar
Create a single-sided trust under the NT4 Domain User Manager, then execute:
root# net rpc trustdom establish domain_name
It works with Samba-3 and NT4 domains, and also with Samba-3 and Windows 200x ADS in mixed mode. Both domain controllers, Samba and NT must have the same WINS server; otherwise, the trust will never work.